Viruses
The core theory of computer viruses has been with us for as long as we've had computers - the simple concept of computer code that can replicate itself, whether or not it is designed to be malicious. The term "virus" would be attached to this type of code much later.
The Creeper virus was first detected on ARPANET, the forerunner of the Internet, in the early 1970s. Creeper was an experimental self-replicating program written by Bob Thomas at BBN Technologies in 1971. It used the ARPANET to infect DEC PDP-10 computers running the TENEX operating system. Creeper gained access via the ARPANET and copied itself to the remote system where the message, "I'm the creeper, catch me if you can!" was displayed. The Reaper program was created to delete Creeper.
In 1982, a program called Elk Cloner was the first personal computer virus to appear "in the wild" (that is, outside the single computer or computer lab where it was created). Written in 1981 by Richard Skrenta, a ninth grader at Mount Lebanon High School near Pittsburgh, it attached itself to the Apple DOS 3.3 operating system and spread via floppy disk. On its 50th use the Elk Cloner virus would be activated, infecting the personal computer and displaying a short poem beginning "Elk Cloner: The program with a personality."
Viruses on the PC
The most common types of virus seen on early PCs were the:
- Boot sector virus - the virus code resides on the floppy or hard disk's boot sector or master boot record (MBR)
- File virus - the code resides within a file, which could be executable or not
- Memory-Resident virus - remains in RAM
The first IBM PC virus in the "wild" was a boot sector virus dubbed (c)Brain or Pakistani Brain, and was created in January 1986 by two brothers, Amjad and Basit Alvi who lived in Lahore, Pakistan.
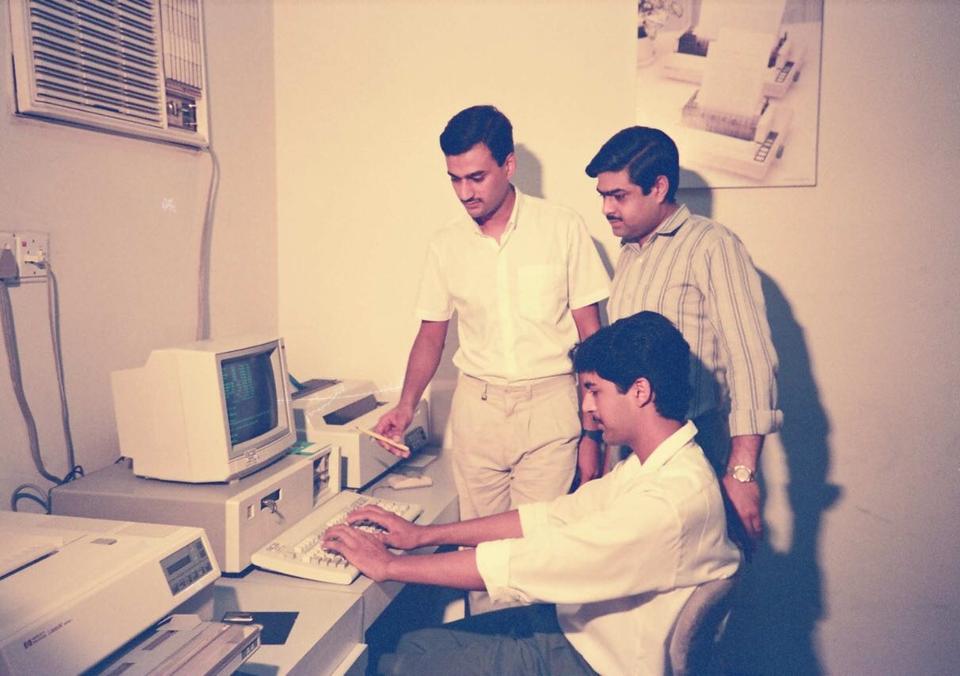
Amjad Alvi and his brothers working at a PC in their father's clinic
Amjad and his younger brother discovered that they could substitute their own program for the executable code present on the boot sector of every floppy disk formatted with Microsoft’s MS-DOS, whether or not it included system files. Users thereby loaded the virus into memory every time they started their computers with any formatted disk in their floppy drives. Once in memory, a virus can copy itself to boot sectors on other floppy or hard disks.
The authors of the Brain virus reportedly created the code to deter unauthorized copying of the software they had written. Shortly after, their code was found on floppy disks at the University of Pittsburgh, Pennsylvania, Delaware and George Washington University. It also slowed systems at the Providence Journal-Bulletin newspaper and popped up in trading terminals in Hong Kong. Users found it on their personal computers in places as far as Australia.
In the case of Brain, it was obvious who had written it, as Amjad had put his address and phone number into the code. Brain was a benign virus as it wasn’t written to erase data or damage hardware. The Alvi brothers had been asked to write a patient management programme (their father was a medical doctor), but they were being paid very little. So they copied Brain onto their floppy disk, explicitly telling their NGO customer not to give it to anyone. Despite his warning the infected floppy was apparently shared, copied and the virus started to move and take on a life of its own. Within a few months it opened the floodgates for newer variants and copycats who applied the same logic as Amjad’s to infiltrate computers and cause widespread damage.
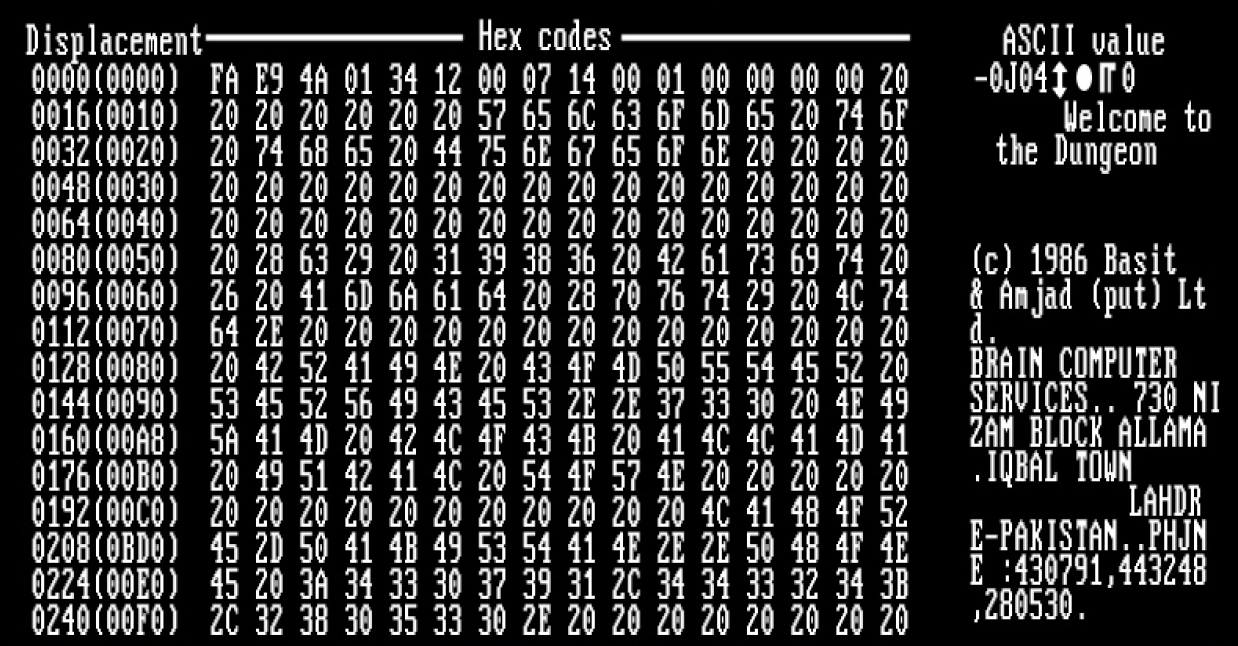
The Brain virus boot sector code with readable advertisement for their services!
With their advertisement, Brain pioneered another characteristic feature of modern viruses: the payload. The payload is the prank or malicious behavior that, if triggered, causes effects that range from annoying messages to data destruction. It’s the virus characteristic that draws the most attention - many virus authors now write their viruses specifically to deliver their payloads to as many computers as possible
Most viruses attempt to avoid detection. They do this through a variety of creative ways. File viruses may go unnoticed because the size of the file they have infected does not grow and/or the date/time stamp remain unaltered when it first gets infected. Memory-resident viruses will sometimes attempt to stop anti-virus programs from running.
Polymorphic Viruses
When anti-virus programs came into more widespread use, virus writers came up with a new term: 'polymorphic'. A polymorphic virus is one that can adapt to the various defenses you impose. Each time a polymorphic virus infects a computer, it creates a modified version of itself to avoid detection but retains the same basic program after each infection. In order to change its physical file composition during each infection, the polymorphic virus encrypts its code and adopts a different encryption key each time. The '1260' virus, written by Mark Washburn is considered the first one that used polymorphism. He did this while analysing the Cascade and Vienna viruses with Ralf Burger in 1989. Ralf had disassembled Vienna allowing Mark to see how it had been constructed. He added a cypher which varied the new virus's signature by randomising its decryption algorithm, and in so doing, anti-virus software that was simply looking for a known signature would be unable to detect it. 1260 was, likeVienna, a memory-resident virus that infected .COM files.
Heuristic Analysis
The advent of polymorphic viruses meant that the traditional method of virus detection, that of looking for a specific signature (a set of known consecutive bytes), was no longer going to work. Anti-virus programs needed a new approach. This was to use heuristics - basically to look for code that exhibited suspicious behaviour, and if found, identify that code as a virus. The problem with this approach was that it could easily generate false positives. If a program has code that deletes a file, for example, it may be considered a virus when it's actually a file/disk utility.
Anti-Virus Software
Some of the more prominent anti-virus products you could use during the DOS era are listed here. Click on the name to open a dedicated page for each product: